Quantum Computing Could Break Top 1,000 ETH Wallets In Days

A quantum attacker may steal money from the transaction while it is waiting to be processed.
The Google quantum computing team has published a white paper explaining how a sufficiently advanced quantum computer can crack the private keys of Ethereum’s 1,000 richest wallets in less than 9 days, putting more than 20 million ETH at risk.
In addition, the paper presented a timeline that the researchers say leaves no room for complacency.
Google Research Findings
To understand the risks, it helps to know how secure crypto wallets are today. Each wallet has a private key, a secret password type, and a public address that cannot be seen by others. The security system that Ethereum currently uses makes it very difficult to go back from the public address to the private key. Quantum computers, once powerful enough, could break that barrier completely.
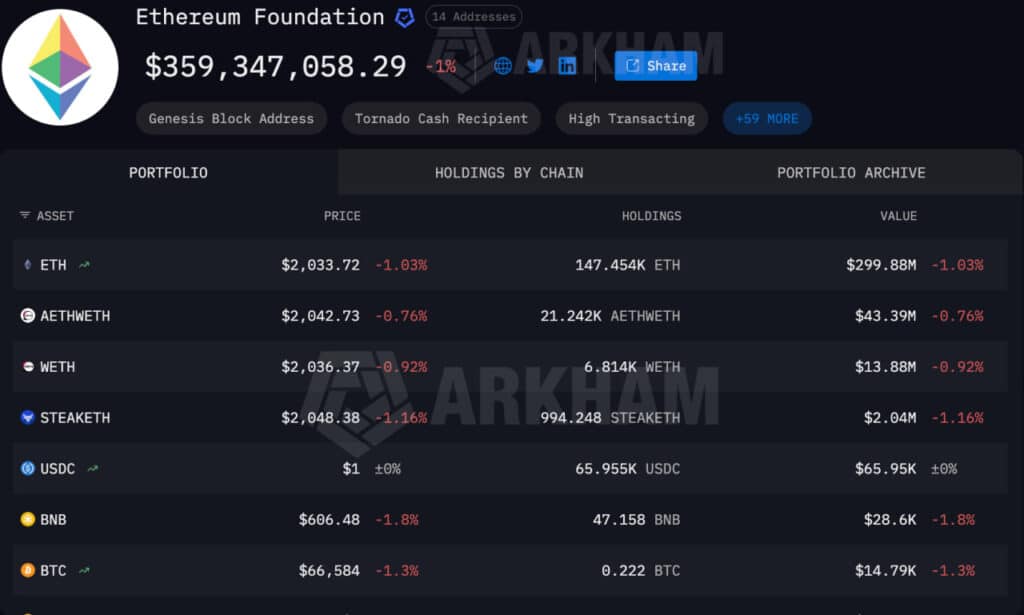
According to Google’s paper, Ethereum is vulnerable on five different levels. The most direct threat to individual wallets: the top 1,000 alone hold about 20.5 million ETH. But smart contracts, the automated systems that power most of Ethereum’s financial operations, are also at risk. Their administrator keys control nearly $200 billion in stablecoins and other real-world assets.
Besides, the guarantors that keep the Ethereum network running hold 37 million ETH in reserves, and the systems that support Ethereum’s Layer-2 networks each carry an exposure worth about 15 million ETH.
The risk isn’t just mental, as Google estimates that a super-fast quantum computer can crack a wallet’s private key in nine minutes. Putting that in the context of Bitcoin will show how dire the situation can be, especially when you remember that a new block of Bitcoin is verified roughly every ten minutes. It means that a quantum attacker could steal money from a transaction that is waiting to be processed before it is deleted. Crypto research group Project Eleven described this as a “mempool attack,” something the crypto community previously thought was far-fetched.
The Warning May Come Too Late
The Google paper puts the qubit requirements for this attack at 1,200 logical qubits and 90 million computational operations or 1,450 logical qubits and 70 million operations, depending on the architecture. According to Project Eleven, this is a 10x improvement over previously published estimates.
You may also like:
Interestingly, on the same day Google released its findings, researchers from Oratomi, Caltech, and UC Berkeley published separate work showing that Shor’s algorithm can work on a cryptographically relevant scale with 10,000 reconfigurable atomic arms, and that ECC-256 could collapse in five days on a 22,000-qubit machine.
However, opinions differ on how imminent the threat is. Some analysts have argued that the risk is at least a decade away and that it will begin to hit the wider internet infrastructure, giving markets time to react. But others are already planning things, Google, for example, sets a deadline of 2029 to improve its systems, and the founder of Ethereum Vitalik Buterin recently published a road map for the network’s quantum resistance, which sets out how its security systems can be changed and those quantum computers will not break.
Binance Free $600 (CryptoPotato Exclusive): Use this link to register a new account and get an exclusive $600 welcome offer on Binance (full details).
SPECIAL OFFER for CryptoPotato readers at Bybit: Use this link to register and open a free $500 position on any coin!